Integrating Enterprise SSO
If you already have an auth provider, but now need to support SAML or Enterprise-level Single Sign-On (SSO), this guide is for you! This guide will cover how to set up your project before you start integrating with your current auth provider.
PropelAuth Configuration
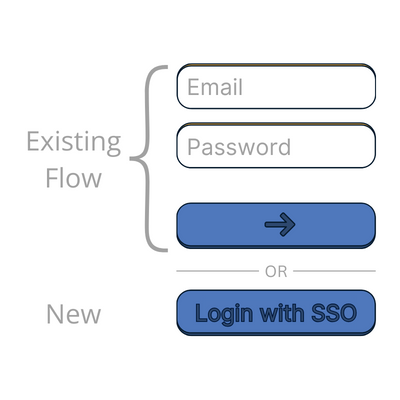
Since you're already integrated with an auth provider, we're assuming you already have a login page. In this guide, we’ll be extending your current auth provider to allow enterprise customers to sign in with their IdP via your login page.
We’ll start with making some changes in the PropelAuth dashboard.
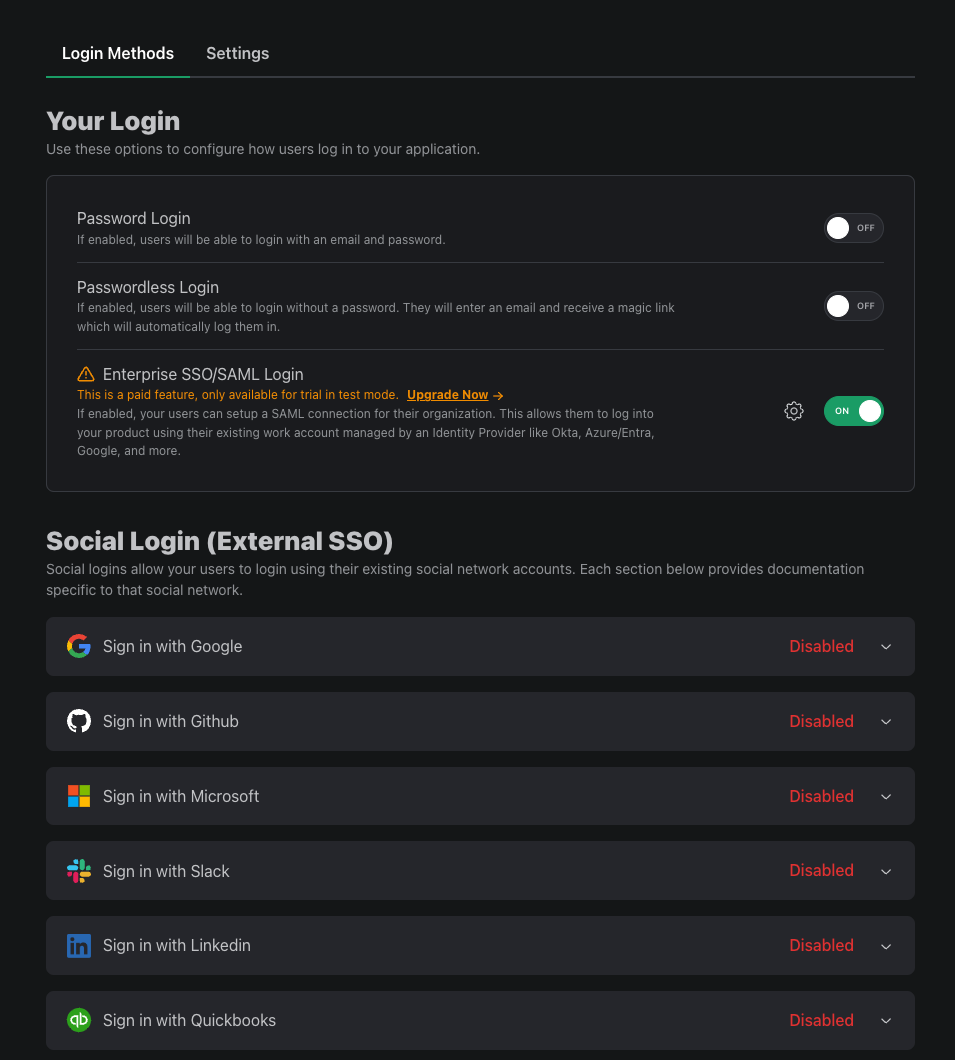
- Update Login Methods - Let’s navigate to the Signup / Login page. Here we can enable SAML but, since you already have other login methods enabled through your auth provider, we can disable every other login method. While we’re here, let’s disable the Allow public signups setting by navigating to the Settings tab.
-
Organization Settings - Head over to the Organization Settings page and disable the Users can create their own orgs setting.
-
(Optional) Setup User Properties - If you have user properties such as name, username, and profile picture that you would like to collect from the IdP, head over to the User Properties page to enable them. You can also create a Custom User Property if you don’t see what you’re looking for.
-
(Optional) Map Roles - If you already have orgs, you likely have roles as well. If you setup that same role structure with us, then your users will be able to show up with role information once they login with SAML. If you’re wanting to use roles, navigate to the Roles & Permissions page and edit or create roles to match your own.
Creating Orgs for your Users
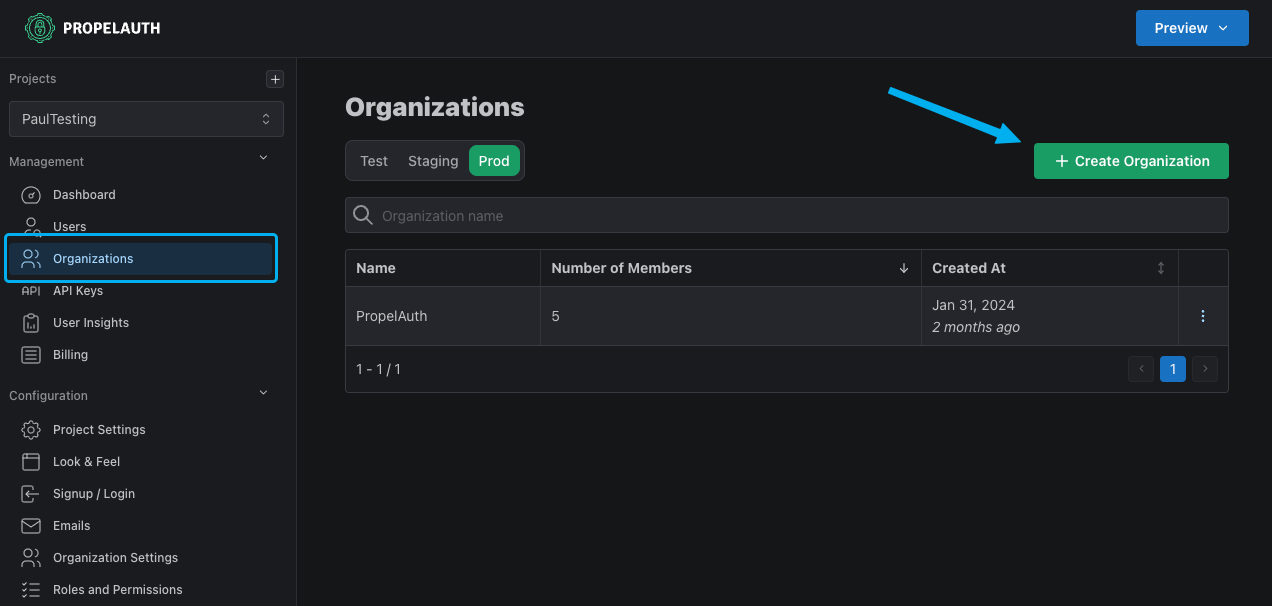
Since SAML is setup on an org to org basis, we need to make sure each user belongs to an org. This can be done manually through the PropelAuth dashboard (via the Organizations page) or programmatically through the PropelAuth API.
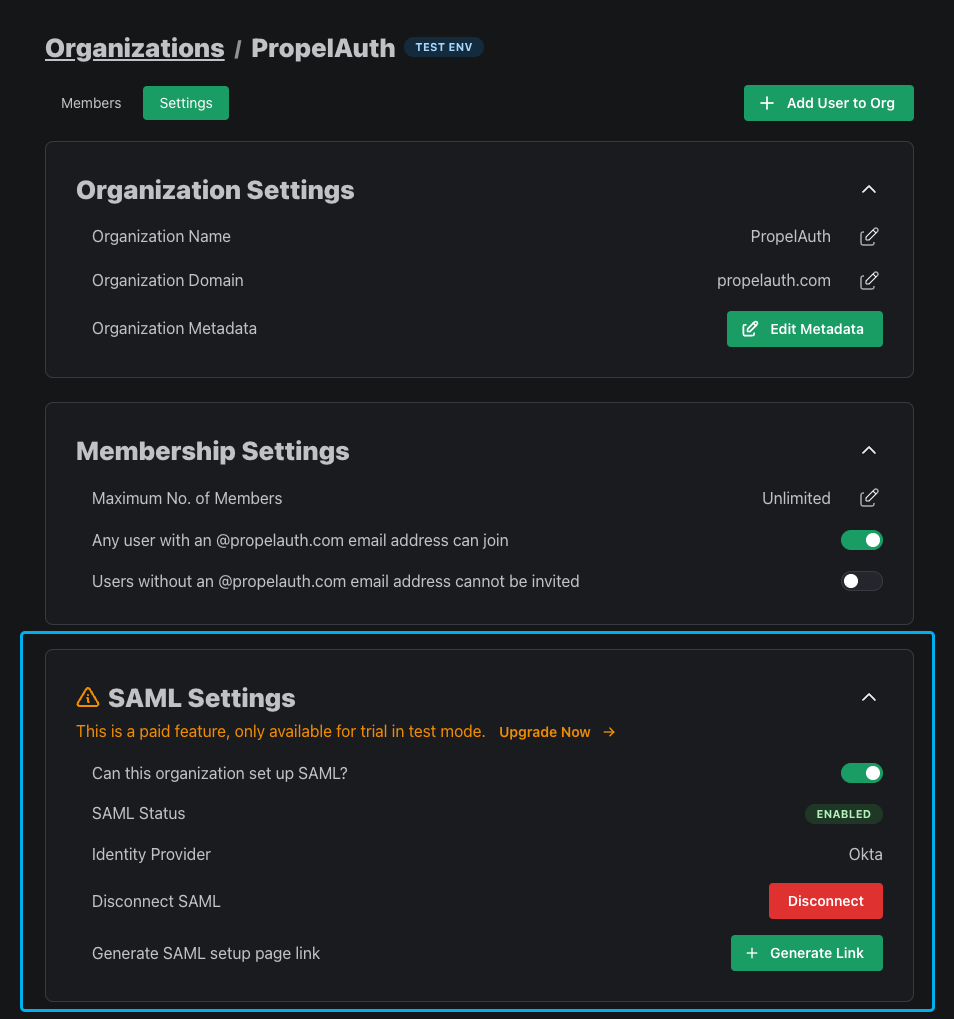
We can then enable SAML for the org. We can do this either in the org’s Settings page or through the API.
Allowing your users to set up their SAML connection
Since SAML is the only enabled login method, we need a way for employees of an organization to set up their SAML connection. To do this, navigate to the Organizations page in your PropelAuth dashboard, find the org, click Settings, and click on the Generate Link button.
This button will generate a link to allow an employee of an organization to set up SAML. This link does not require authentication to access and is intended to be used by an employee of the org, such as a member of their IT team.
Next Steps
You're now ready to start integrating your current auth provider with PropelAuth! Check out these guides for the next steps:
